
Social Network Analysis for Computer Scientists
This course deals with computer science (CS) aspects of social network analysis (SNA), and is open to all students in the master computer science programme at Leiden University.
These pages are being prepared for the Fall 2025 semester...
Course information
Lectures: Fridays from 9:00 to 10:45 in Gorlaeus lecture room BM1.33
Lab sessions: Fridays from 11:00 to 12:45 in Gorlaeus lab room DM0.09 an DM0.17
Prerequisites: a CS bachelor with courses on Algorithms, Data Structures and Data Mining
Literature: provided papers and book chapters (free and digitally available)
Examination: based on presentation, paper, programming, peer review and participation (no exam)
Brightspace link: 2526-S1 Social Network Analysis for Computer Scientists
Study guide link: Social Network Analysis for Computer Scientists
Study points: 6 ECTS
Course staff: dr. Frank Takes (f.w.takes@liacs.leidenuniv.nl, room BE 3.07), Rachel de Jong MSc (room BE 3.03)
Assistants:
Gamal Elgamal MSc (room BE 2.23),
Bart Holterman, Thanos Kalligeris and Bart Westhoff
![[Network visualization image]](yeast_eccs.jpg)
Network with 1458 nodes and 1948 edges.
Course schedule
| Date | Lecture (9:00-10:45) | Lab session (11:00-12:45) | ||
| 1. | Fri Sep 5, 2025 |
Lecture 0: Course information Lecture 1: Introduction and small world phenomenon |
Introduction to Gephi Work on Assignment 1 |
|
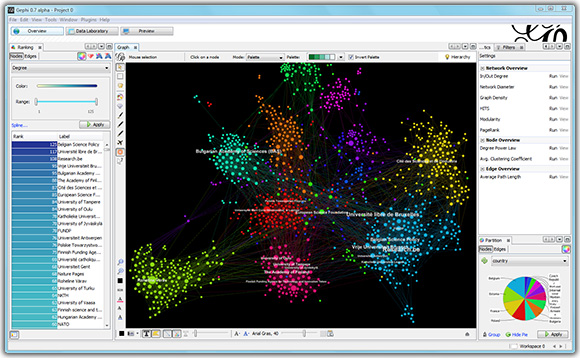
About social network analysis tools and packages. There exist different tools and packages for social network analysis. In this course, we coveR two of them, with complementary advantages:
- Gephi, an easy-to-use tool with a graphical interface useful for visualization
and quick analysis of relatively small network data (this week, see below).
- NetworkX, an extensive Python package for network analysis that can handle larger network datasets and computations (next week).
Learning goals. The main goal of this lab session is to become familiar with Gephi (experimental beta-software to visualize networks for research purposes) and its input format. At the end of this session you should be able to:
- Know how to use Gephi for social network analysis
- Import and visualize raw network data with labeled nodes and labeled and/or weighted edges (directed or undirected),
- Understand how to map edge and node size and color to structural network properties such as the node degree and edge type,
- Know how to apply filters to the visualization, for example to focus only on the giant component,
- Export a vector graphic PDF of your network for reuse in for example a presentation or paper,
- Export computed node data for reuse in another program.
There is no deliverable for this lab session, but you are assumed to know the tool afterwards. Practice more at home if needed.
Instructions:
- Walk through the Gephi tutorial.
Note that the tutorial briefly covers topic such as centrality and communities, that will not be covered extensively until Lecture 2.
Done? Get started with the practical part of Assignment 1. You can download the smaller datafiles medium.tsv and large.tsv. If you want to analyze huge.tsv, you will have to get it from the shared folder in the ISSC Linux or LIACS DS lab environment, as stated in the assignment.
Reading material
Some students have expressed interest in additional reading material to help freshen up on skills and knowledge required for this course.
- To brush up on your Python programming skills, you could do Lecture 0, 1 and 4 of these Scientific Python Lectures.
- To freshen up your LaTeX skills, you could do for example this tutorial (old link, seems ad-infested; choose any other online source).
- MIT has a nice online course on discrete mathematics. Relevant chapters: 5, 6 and 7.
- The (Dutch) Leiden courses Algoritmiek (Algorithms) and Datastructuren (Data structures) might be also interesting to browse through.
- Basic knowledge of concepts in machine learning and data mining are provided, e.g., at the Wikipedia machine learning page.